National network
Canadian dealer-system integration across a distributed retail environment.
Integration Case Study
Turning complex OEM, dealer, and system-provider requirements into workable, secure, and governed integration across a Canadian automotive retail environment.
This case study reflects integration work performed with a major German sports car manufacturer's Canadian national sales company during a period when automotive retail integration was moving from dealer-local, system-specific connectivity toward more centrally governed digital platforms. The delivery approach focused on coordinating integration work between the OEM and Canadian system providers, translating global technical direction into practical, supportable integration across a national dealer environment.
National network
Canadian dealer-system integration across a distributed retail environment.
Hybrid integration
Legacy DMS connectors, local middleware, shared directories, and emerging central platform patterns.
Governed delivery
Provider coordination, testing, issue management, access control, and rollout discipline.
Industry relevance
Practical experience relevant to member-controlled data hubs, vendor access, and secure data exchange.
Executive Summary
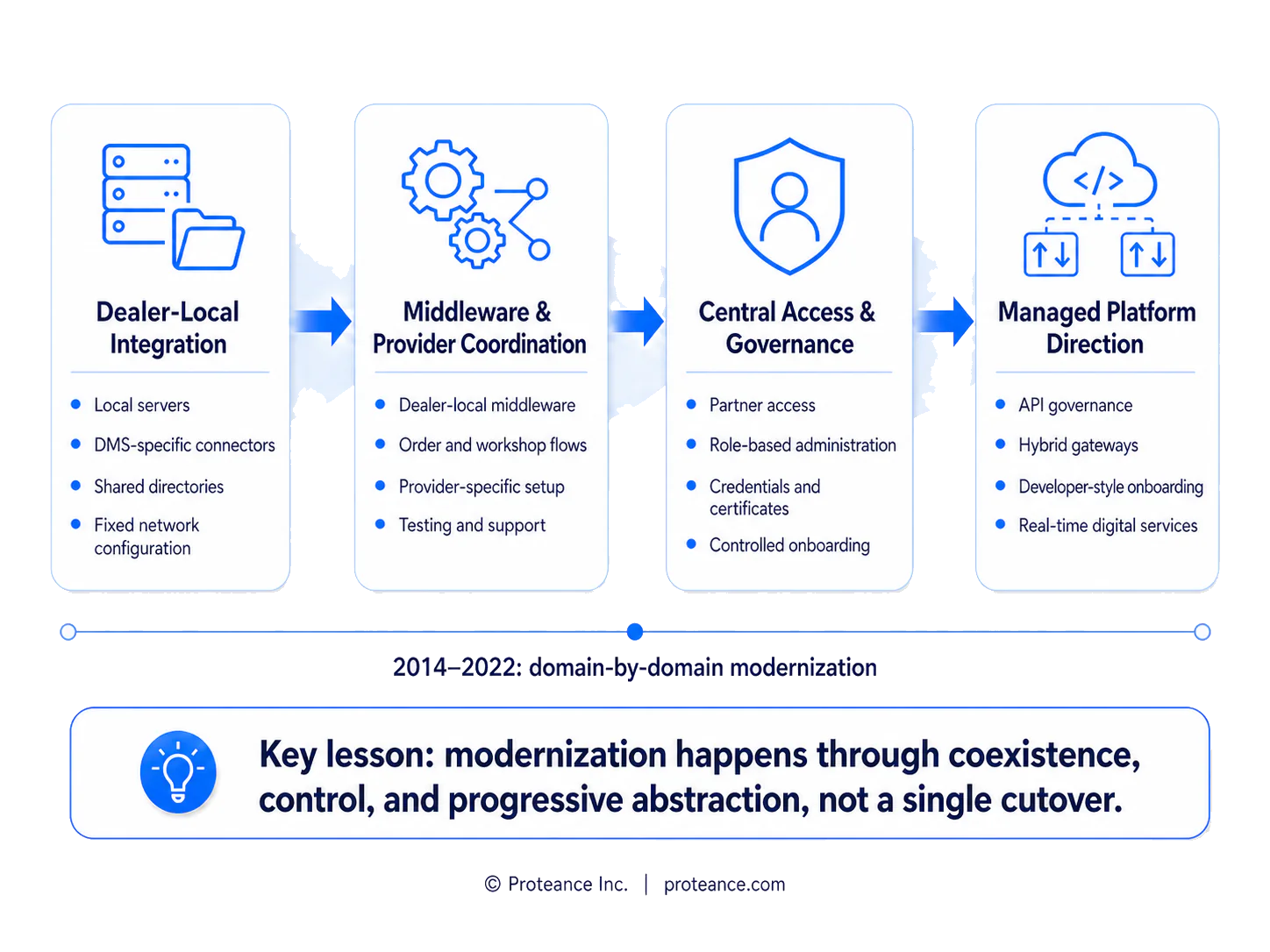
The business and technical context was not a single step from legacy integration to fully modern interfaces. The stronger pattern was layered transition. Parts and workshop integration often remained dependent on dealer-local systems, DMS-specific middleware, shared directories, fixed network configurations, and technical users that supported order-transfer and service workflows.
In parallel, customer, vehicle, partner, and enterprise domains increasingly moved toward centrally governed digital platforms, managed partner identity, hybrid gateways, and structured onboarding. These domains did not modernize at the same speed. Coexistence was normal, not temporary noise.
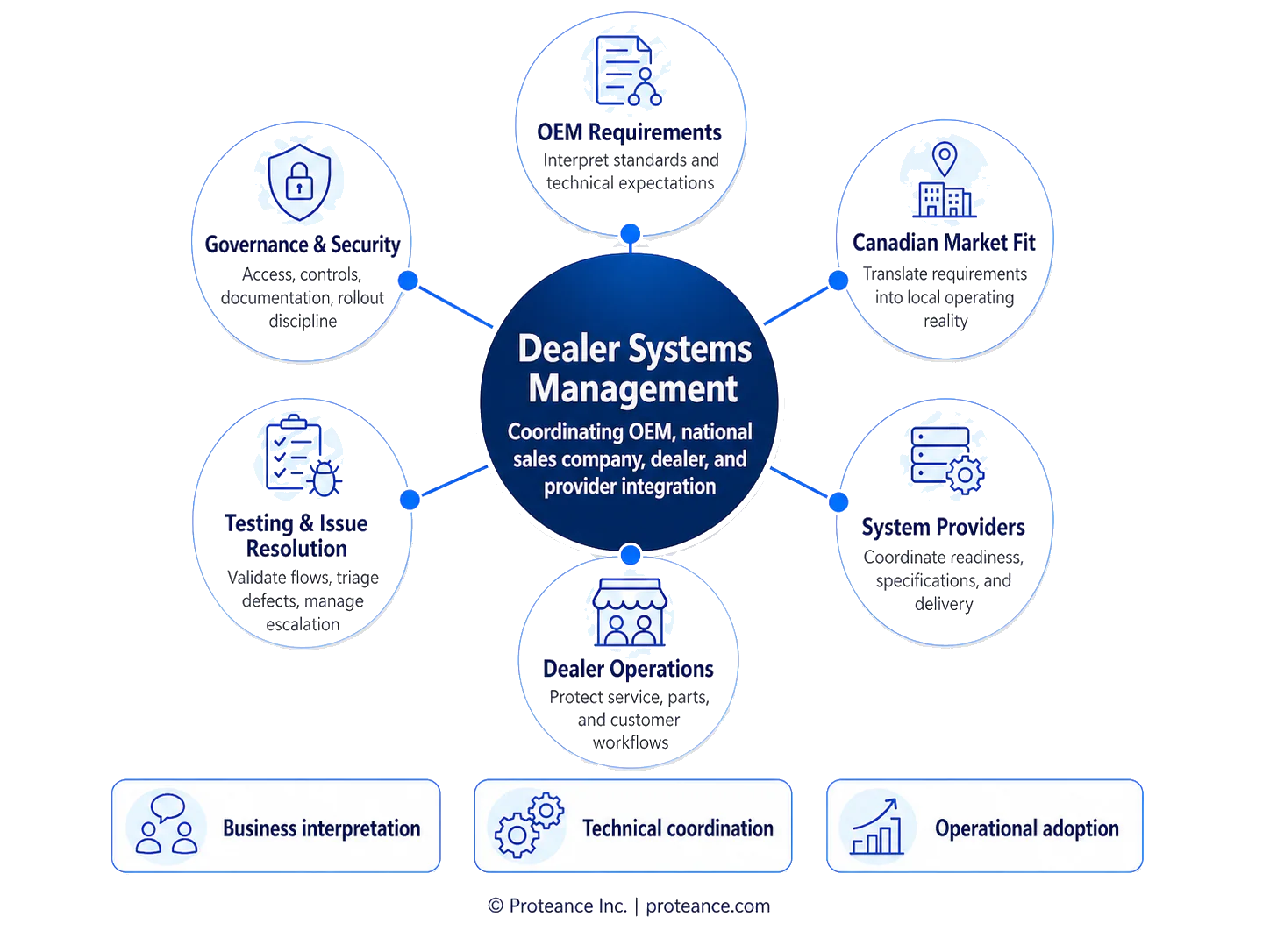
The practical challenge was therefore not only connectivity. It was integration governance across the OEM, the national sales company, dealers, DMS providers, system vendors, security controls, and day-to-day operational workflows. Delivery required aligning technical implementation with commercial and service continuity.
Successful integration depended on understanding how data actually moved, how dealers relied on that movement, where failure points appeared, and how change could be managed without disrupting local operations. This experience now informs how Proteance approaches complex integration and governed data exchange in automotive environments.
Delivery Perspective
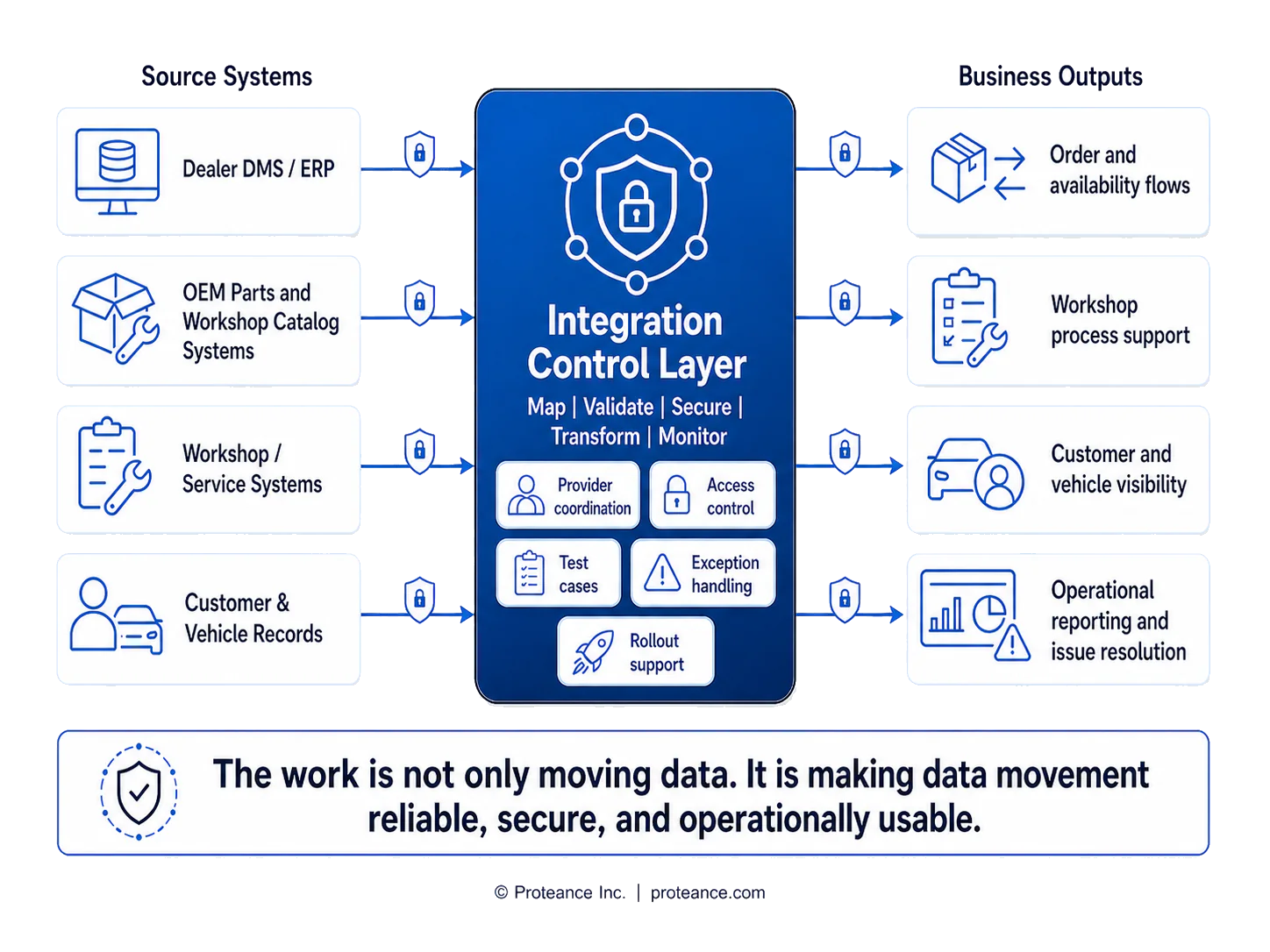
Proteance applies a practical integration pattern shaped by this experience. Work starts with operational reality rather than abstract target-state diagrams. Existing system dependencies are mapped first, then critical control points are defined for ownership, access, testing, and escalation.
Provider coordination is treated as a core delivery stream. Secure access design is addressed early, with clear authorization boundaries and supportable control models. Testing is deliberate and tied to operational outcomes, not only technical checks.
Transition from pilot to production is governed through readiness, defect pathways, and support discipline. The objective is controlled modernization that preserves business continuity while improving integration quality and governance maturity.
Situation
Dealer systems and Canadian providers had to support requirements from a major German sports car manufacturer. Parts, workshop, customer, vehicle, and order-related flows depended on systems that were not all modern APIs. Dealer-local components, DMS-specific connectors, folder-based exchanges, network controls, technical users, and centrally governed services coexisted.
Different domains modernized at different speeds. In practical terms, OEM parts and workshop catalog systems, dealer-local integration middleware, the OEM customer and vehicle digital ecosystem, and the OEM partner access platform all had to be understood together.

Business Problem
The system landscape was fragmented. If integrations failed, dealer operations could be disrupted quickly across parts, workshop, customer, vehicle, and service processes. Multiple vendors and providers worked with different capabilities and delivery maturity.
Security and access requirements had to be managed across organizations, not only within one system. Data movement needed to remain accurate and supportable while global OEM direction was interpreted for Canadian market realities.
The core risk was loss of control: unclear ownership, delayed issue resolution, and integration designs that did not hold in real dealer operating conditions.
Role and Contribution
Integration delivery at the OEM Canadian national sales company required coordinating work between the OEM and Canadian system providers. The role required translating OEM requirements into practical provider action while maintaining dealer-system usability.
Contribution included coordinating DMS and provider readiness, managing testing, supporting issue resolution and escalation, sequencing rollout, and integrating operational feedback into delivery plans. Global standards were balanced with Canadian dealer-system realities to keep integrations workable, supportable, secure, and operationally usable.
Solution Pattern
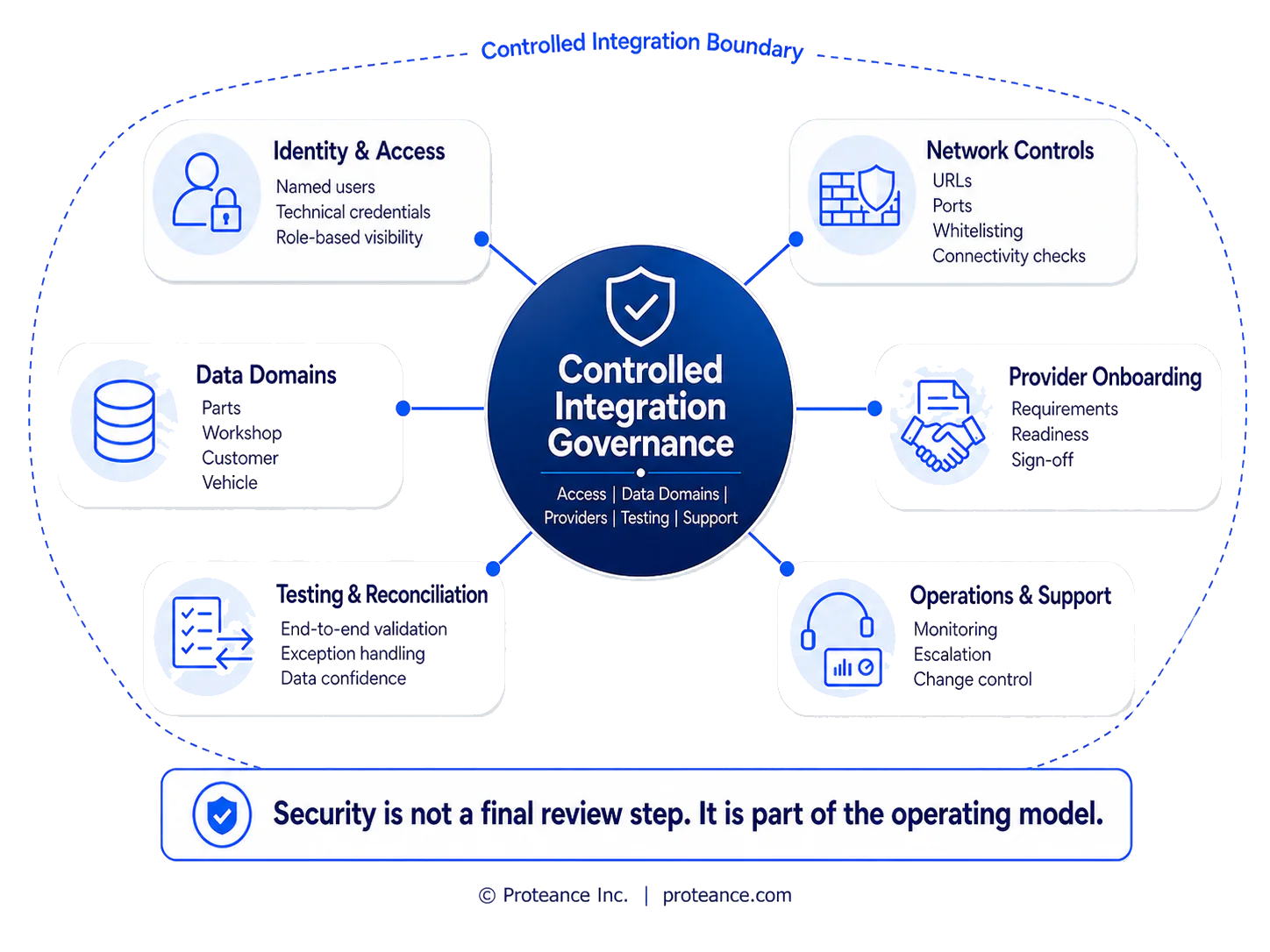
Security, Governance, and Controlled Access
Security was not treated as a separate final review. It was part of daily integration governance. This included named access and technical users, provider onboarding and authorization discipline, and careful awareness of firewall, URL, port, and network dependencies.
Control meant knowing who could connect, which systems could exchange, and which data domains were in scope. Documentation, escalation pathways, auditability, and support readiness were essential to maintaining controlled delivery across organizations.
Transformation
No unsupported performance claims are made. The practical impact was operational. Coordination became more structured across OEM, national sales company, dealer, and provider parties. Integration ownership and issue routes became clearer.
Dealer operations were better supported through technical change, and the environment gained a stronger base for future governance and platform modernization. The key capability developed was managing coexistence between local integration dependencies and emerging central governance direction.
Why This Matters for Industry Data Governance
Proposed member-controlled industry data platforms require controlled data movement, integration with existing local systems, vendor access governance, secure Canadian-hosted infrastructure, data normalization, auditability, and staged adoption.
This founder-led automotive experience is relevant because it demonstrates how to manage the difficult middle ground between legacy operational systems and governed central platform direction.
Practical parallels
What This Experience Demonstrates
This founder-led experience shows why Proteance approaches data platforms as operating systems, not just software builds. The real work is understanding who owns the data, how it moves, who can access it, how it is protected, how vendors are governed, and how the solution can be adopted without disrupting day-to-day operations.
Request a BriefingBoard appendix diagrams
This website version includes the five core diagrams used in the narrative. If needed, we can add two appendix visuals covering automotive data-flow control points and pilot-to-production delivery stages.
Disclaimer
This case study reflects anonymized founder-led experience from work performed before Proteance was formed. The automotive manufacturer and related entities have been intentionally anonymized. The case study is presented to illustrate relevant automotive integration, dealer-system, data governance, security, and operational delivery experience. It does not disclose confidential manufacturer information and should not be read as a claim that Proteance implemented the OEM's global systems, central platforms, API program, or enterprise integration architecture. It also does not imply endorsement by, affiliation with, or approval from the OEM or any related entity.